Amid the wave of digital transformation, the security surveillance industry is undergoing a paradigm shift from passive recording to proactive protection. According to MetaTech Insights, the global smart security market reached $74.53 billion in 2024 and is projected to grow to $292.9 billion by 2035, with a compound annual growth rate of 13.25%. Behind this explosive growth lies the deep integration of three core technologies: Artificial Intelligence (AI), Internet of Things (IoT), and Cloud Computing — together building the technical ecosystem of Intelligent Vision-Cloud-Connectivity, which empowers surveillance systems with real-time perception, intelligent cognition, and collaborative decision-making capabilities.
The core limitation of traditional surveillance systems is post-incident review: massive video data is stored but rarely analyzed in real time. After a security incident, staff must manually review hours or even days of footage. In contrast, the new generation of intelligent security systems, built on the AIoT (AI + IoT) architecture, achieves closed-loop management: pre-warning, in-process intervention, and post-incident traceability. Edge AI chips equip front-end devices with real-time analysis capabilities, cloud computing provides massive data storage and deep learning power, and 5G networks ensure low-latency transmission. Together, they boost monitoring efficiency dozens of times over.
This article deeply analyzes the technical architecture, core application scenarios, and industrial practices of Intelligent Vision-Cloud-Connectivity, revealing how this security revolution redefines the boundaries of safety.
Technical Architecture: An Intelligent Perception Network with Cloud-Edge-Device Collaboration
Edge Intelligence: The Front-End Revolution Empowered by AI Chips
The combination of edge computing and AI chips forms the first line of defense for intelligent security. Traditional surveillance cameras only act as “eyes” to capture images, with all analysis relying on cloud processing — resulting in high bandwidth pressure, long latency (often hundreds of milliseconds), and significant privacy risks. Embedded AI chips (such as Huawei Ascend, Horizon Robotics Journey, and Cambricon MLU series) transform cameras into intelligent terminals with a “brain.”
Edge computing offers three core advantages:
Ultra-low latency: End-to-end response time within 50 milliseconds, suitable for highly real-time scenarios such as autonomous driving assistance and industrial quality inspection.
Privacy security: Raw video remains local; only structured data (e.g., “car – Beijing N8XXXX – white – 52km/h – running red light”) is uploaded to the cloud, complying with GDPR, CCPA, and other international privacy regulations.
Flexible deployment: Devices operate independently without relying on networks or central servers, ideal for remote areas or unstable network environments.
Technically, edge AI uses lightweight neural network models (e.g., YOLOv5s, MobileNetV3, EfficientNet-Lite). Through model compression and quantization, it achieves face detection, behavior recognition, vehicle analysis, and other functions with limited computing power. AI chips dedicated to security from Hisilicon, Horizon Robotics, and others consume less than 5W and deliver over 4 TOPS of computing power, supporting real-time analysis of 1080P video streams.
Edge Nodes: Intelligent Gateways for Regional Collaboration
As a bridge between cloud and devices, edge nodes undertake data aggregation, preprocessing, and regional collaboration. In large campuses or urban scenarios, uploading raw video streams from hundreds of cameras directly to the cloud would cause severe network congestion and storage pressure. Edge nodes filter redundant data (e.g., static scenes, normal traffic) through local AI inference, uploading only short clips and structured labels of abnormal events (intrusion, fire, crowd gathering), reducing bandwidth usage by over 90%.
Edge nodes include edge servers, AI computing boxes, and intelligent gateways. The NVIDIA Jetson TX2, for example, integrates a 6-core CPU, 256-core GPU, and 8GB RAM, processing 4 channels of 1080P video simultaneously at 12 FPS using TinyYOLOV3, suitable for forest fire prevention and traffic monitoring. Advanced edge nodes support containerized deployment (Docker/Kubernetes), enabling fast iteration and elastic scaling of algorithm applications.
Cloud Platform: The Empowerment Center for Big Data and Deep Learning
Cloud computing delivers three core capabilities for intelligent security:
Massive storage: Tiered storage strategy — hot data (last 30 days) on object storage, warm/cold data automatically archived to low-cost storage, cutting costs by up to 70%.
Deep analysis: Cloud GPU clusters run complex models (ResNet-152, Transformer) for cross-camera tracking, long-term behavior analysis, and billion-level face database matching — tasks beyond edge capabilities.
Model training: Federated learning aggregates data features (not raw video) from multiple edge nodes to continuously improve AI model accuracy.
The cloud-edge collaboration architecture follows the principle of inference at the edge, training in the cloud. Edge nodes perform real-time object detection; the cloud conducts correlation analysis and model optimization, then pushes updated models back to edges. This closed loop enables continuous evolution. For instance, a retail chain’s security system trained a dedicated model for “unscanned exit” using nationwide edge data, raising accuracy from 72% to 96%.
Core Application Scenarios: Intelligent Leap from Security to Operations
Smart Cities: The Nerve Center of Global Perception
In urban governance, the Intelligent Vision-Cloud-Connectivity architecture builds a city-wide retina. Taking Huawei Cloud IEF as an example, edge-deployed video preprocessing nodes enable real-time anomaly detection in parks, residences, and supermarkets: edge AI identifies fights, illegal gatherings, traffic accidents, triggers local alarms, and uploads to the cloud; the cloud performs cross-camera tracking, behavior pattern analysis, and predictive early warning.
China Tower uses its nationwide tower resources to deploy edge computing nodes and thermal imaging cameras, covering 3–10 km per unit for full-area forest fire monitoring. Edge nodes run fire and smoke detection algorithms for instant response, while the cloud continuously optimizes model accuracy.
In traffic management, AI systems analyze real-time traffic flow and dynamically adjust signal cycles. ANPR and behavior analysis automatically detect illegal parking, wrong-way driving, and emergency lane occupation. Hanwha Vision’s SightMind platform integrates urban CCTV data to detect illegal dumping and road damage, improving response speed by more than 10 times.
Smart Retail: From Security to Business Intelligence
In retail, intelligent vision systems create value beyond security. Cameras analyze customer paths, dwell time, and product interactions to generate heatmaps and conversion funnels, optimizing shelf layout and marketing strategies. The cloud aggregates multi-store data to identify regional consumption trends and guide inventory allocation.
Edge nodes run lightweight Re-ID (person re-identification) to track in-store journeys; the cloud performs cross-store passenger flow analysis and member recognition. After deployment, an international apparel brand optimized fitting room locations and sales strategies, boosting single-store sales by 18%.
Industrial Safety: A New Paradigm of Predictive Protection
Industrial environments demand ultra-high real-time performance and reliability. The architecture fuses video, sensor, and control data for multi-dimensional risk early warning. In chemical parks, edge nodes process temperature, pressure, vibration, and video simultaneously: if temperature exceeds thresholds and smoke is detected, the system judges fire risk, triggers fire linkage, and alerts managers instantly.
Typical applications:
Hard hat detection: AI identifies workers without helmets, alarms locally, and records violations.
Post desertion detection: Monitors key positions to prevent accidents from negligence.
Fire lane obstruction detection: Automatically identifies blocked passages and alerts immediately.
These applications shift from post-incident accountability to pre-incident prevention, drastically reducing accident rates.
Finance & Critical Infrastructure: High-Level Security Systems
Banks, data centers, and critical infrastructure impose strict security and compliance requirements. Multi-modal biometrics (face + iris + behavior) and edge-side encryption build high-level protection. Video features are extracted locally; only encrypted vectors are uploaded, while raw footage stays on-site, satisfying financial regulatory data sovereignty and privacy rules.
5G enhances mobile surveillance: 5G body cameras stream live video to command centers, supporting AR remote assistance. Edge computing ensures priority transmission for critical streams within 20ms latency under network slicing.
Key Technological Breakthroughs: Integrated Innovation of AIoT
Video Structuring: From Pixels to Semantic Data
Video structuring is the core technology, converting unstructured video into searchable, analyzable structured data. Edge AI chips run detection, tracking, and recognition to extract attributes of people, vehicles, and objects, recording spatiotemporal trajectories. Structured data accounts for only 1% of raw video but carries over 90% of effective information.
Evolution directions:
Multi-Object Tracking (MOT): Stable tracking of hundreds of targets in dense scenes.
Cross-camera Re-ID: Continuity via appearance and posture.
Behavior understanding: From “person fallen” to “suspected fight.”
Digital Twin & Virtual Inspection
Digital twin maps physical spaces into virtual models for remote immersive inspection. Integrating BIM and real-time video, managers view cameras virtually, simulate evacuation routes, and optimize layouts. In data centers, digital twins unify IT equipment and physical security visualization.
Privacy Computing & Compliance
With laws like the Personal Information Protection Law, privacy protection is mandatory. Federated Learning allows multi-party joint training without sharing raw data: edges train locally, upload parameter updates, and the cloud aggregates a global model. This “data stays, models move” model protects privacy while improving generalization.
Homomorphic encryption and differential privacy anonymize video for encrypted analysis, meeting finance and healthcare compliance.
Industrial Ecosystem and Standardization
Major Players and Technical Routes
The global smart security market is moving toward full-stack cloud-edge-device layout:
Huawei: End-to-end solutions with Ascend chips and HarmonyOS.
Hikvision, Dahua: Self-developed AI chips to strengthen edge intelligence.
Hanwha Vision: SightMind cloud platform for cloud-edge analytics.
Horizon, Cambricon: Algorithm + chip modules for small security enterprises.
Technical routes:
Edge-first: Max front-end computing for privacy-sensitive areas.
Cloud-edge collaboration: Edge for real-time response, cloud for complex analysis — mainstream today.
Cloud-only: Shrinking share as edge chips become cheaper.
Standardization and Interoperability Challenges
Large-scale deployment faces fragmented standards. ONVIF and GB/T 28188 solve device access, but AI interfaces, cloud-edge protocols, and data semantics remain inconsistent. The industry is promoting ONNX for model standardization and KubeEdge / EdgeX Foundry for edge frameworks to reduce integration complexity.
Future Outlook: From Perceptual to Cognitive Intelligence
Large Models and Generative AI
Since 2024, LLMs and VLMs have entered security. GPT-4V, Claude 3 enable natural language video search (e.g., “find people in red entering the warehouse yesterday”). Future systems will use “large model brain + small model edge” architecture.
Generative AI creates synthetic data for rare-scenario training (e.g., fires in extreme weather) and virtual environments for testing.
Autonomous Security and Robot Collaboration
Next-gen security evolves to autonomy: edge AI not only detects threats but also acts — locking areas, deploying drones, guiding security robots. The “perception-cognition-action” loop upgrades systems from tools to active defenders.
Global Interconnection and Ecosystem Integration
With Matter and 5G-A, security will deeply integrate with smart homes, cities, and industrial networks. Home cameras, car recorders, wearables form a ubiquitous perception network. Federated learning shares intelligence across the cloud, building a “everyone participates, everywhere perceives” safety ecosystem.
Conclusion: Intelligent Vision-Cloud-Connectivity Defines a New Security Paradigm
The deep integration of AI, IoT, and cloud computing is reshaping security surveillance. From edge perception to cloud analysis and cloud-edge collaboration, Intelligent Vision-Cloud-Connectivity turns surveillance from a cost center into a value center — ensuring safety while empowering business intelligence, urban governance, and industrial optimization.
Deloitte forecasts that by 2025, AI-driven video analytics will generate hundreds of billions of dollars annually. As edge computing, large models, and privacy computing advance, intelligent security will enter a new era of cognitive intelligence, building a safer, smarter world. This technology-driven revolution will finally complete the leap from “seeing risks” to “foreseeing the future”.
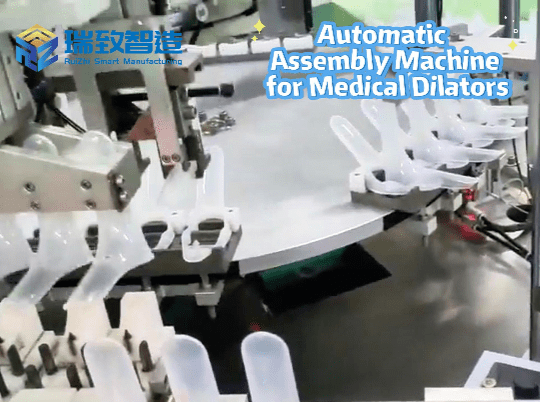
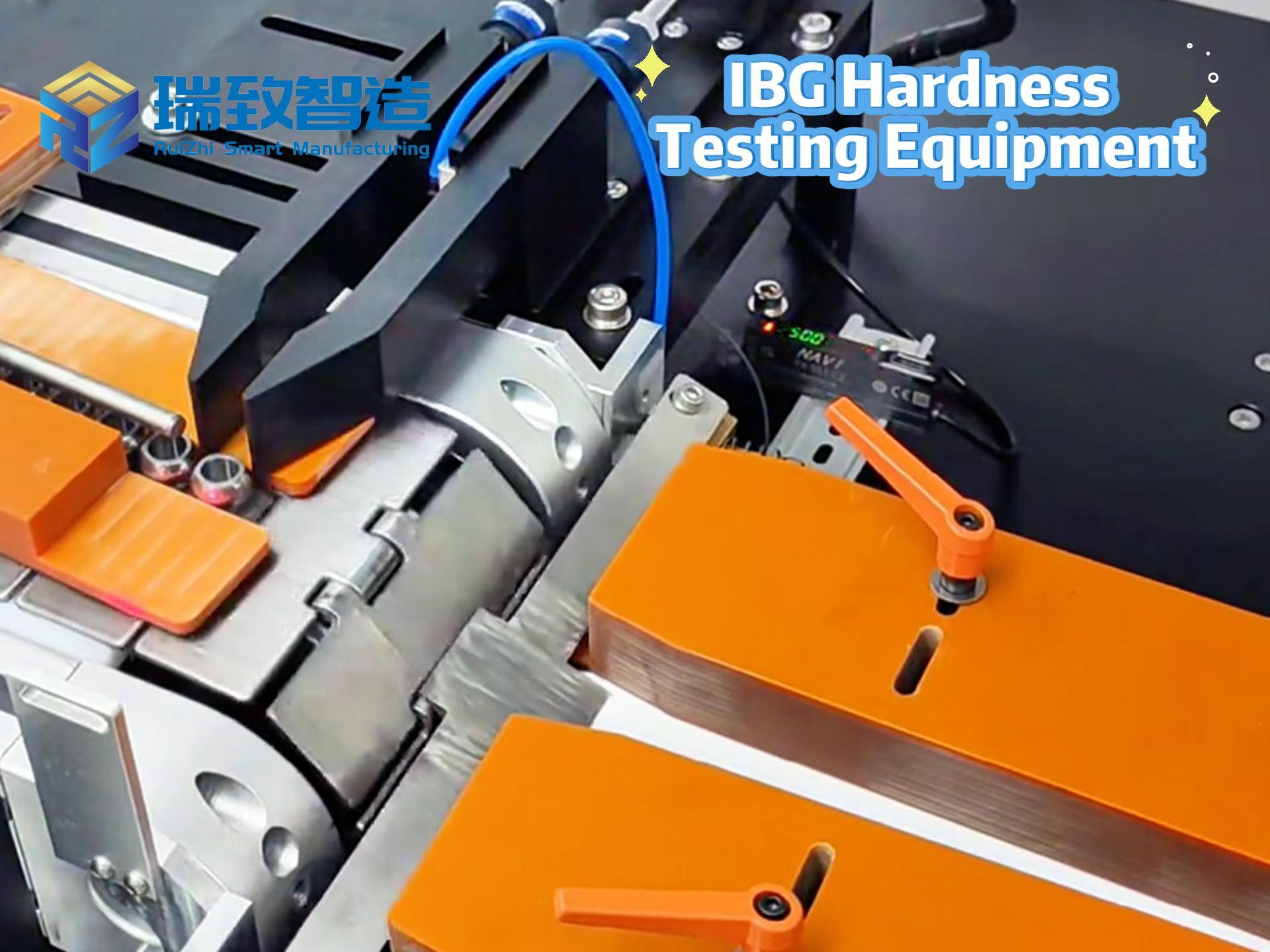
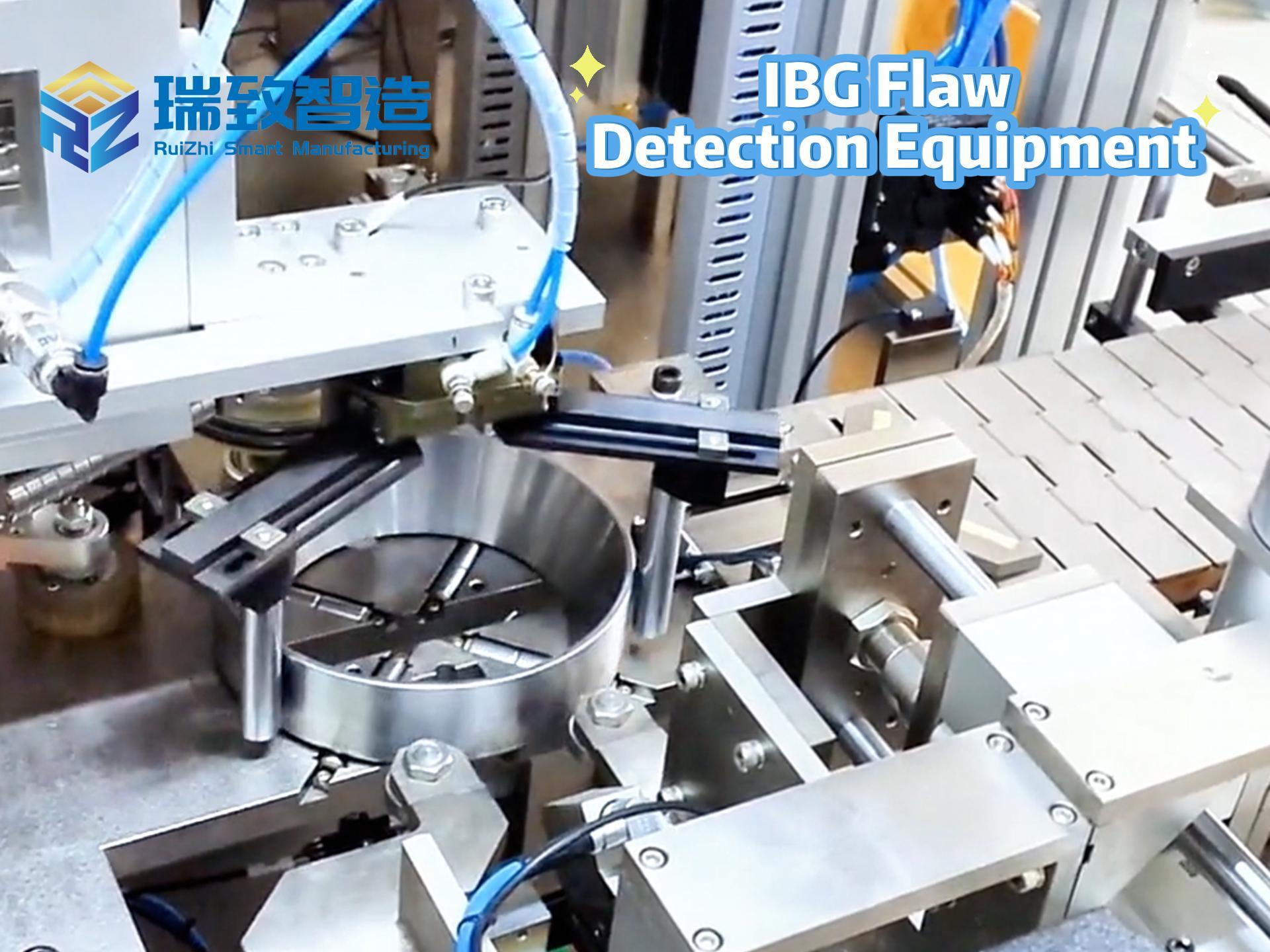
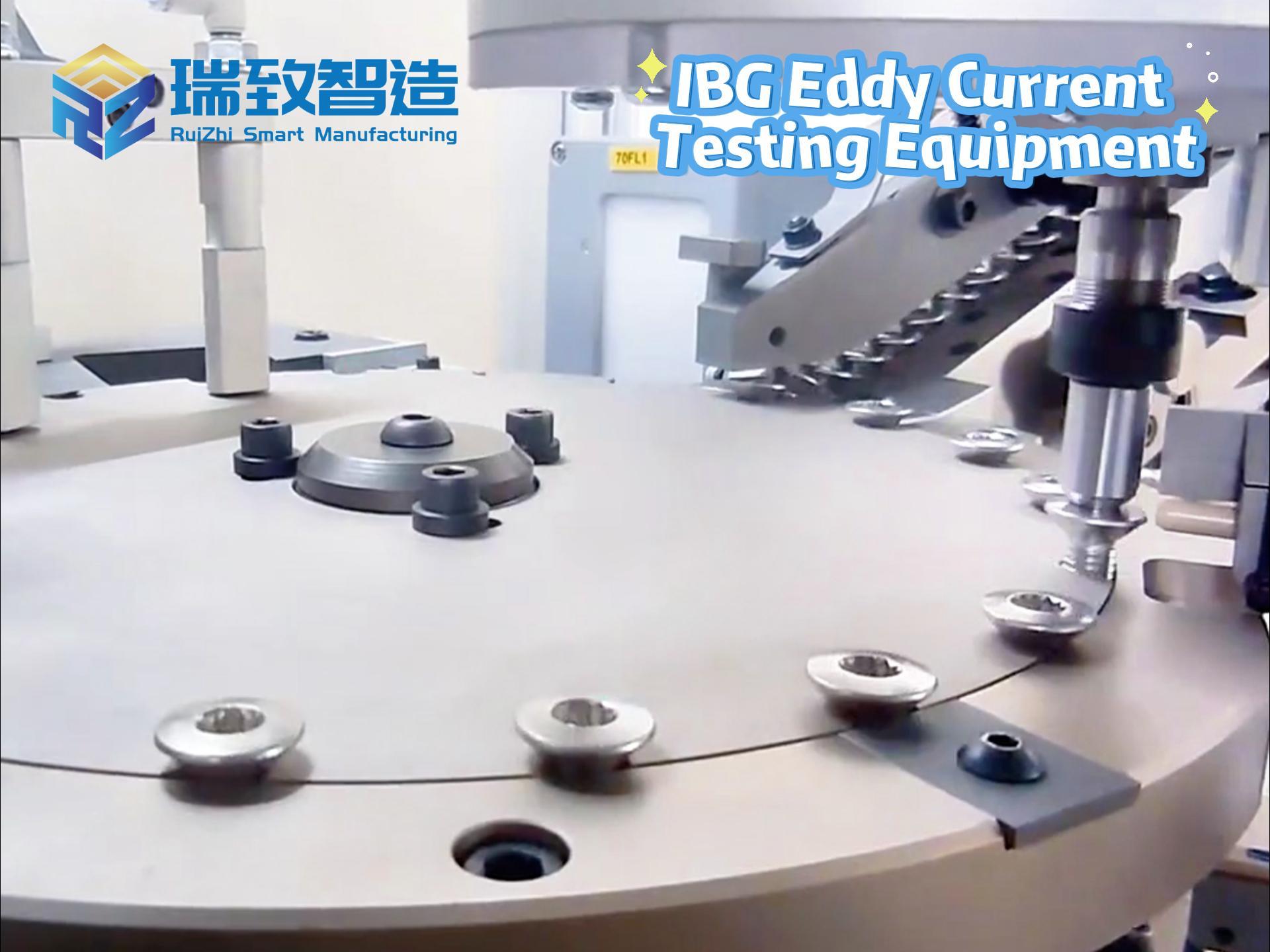
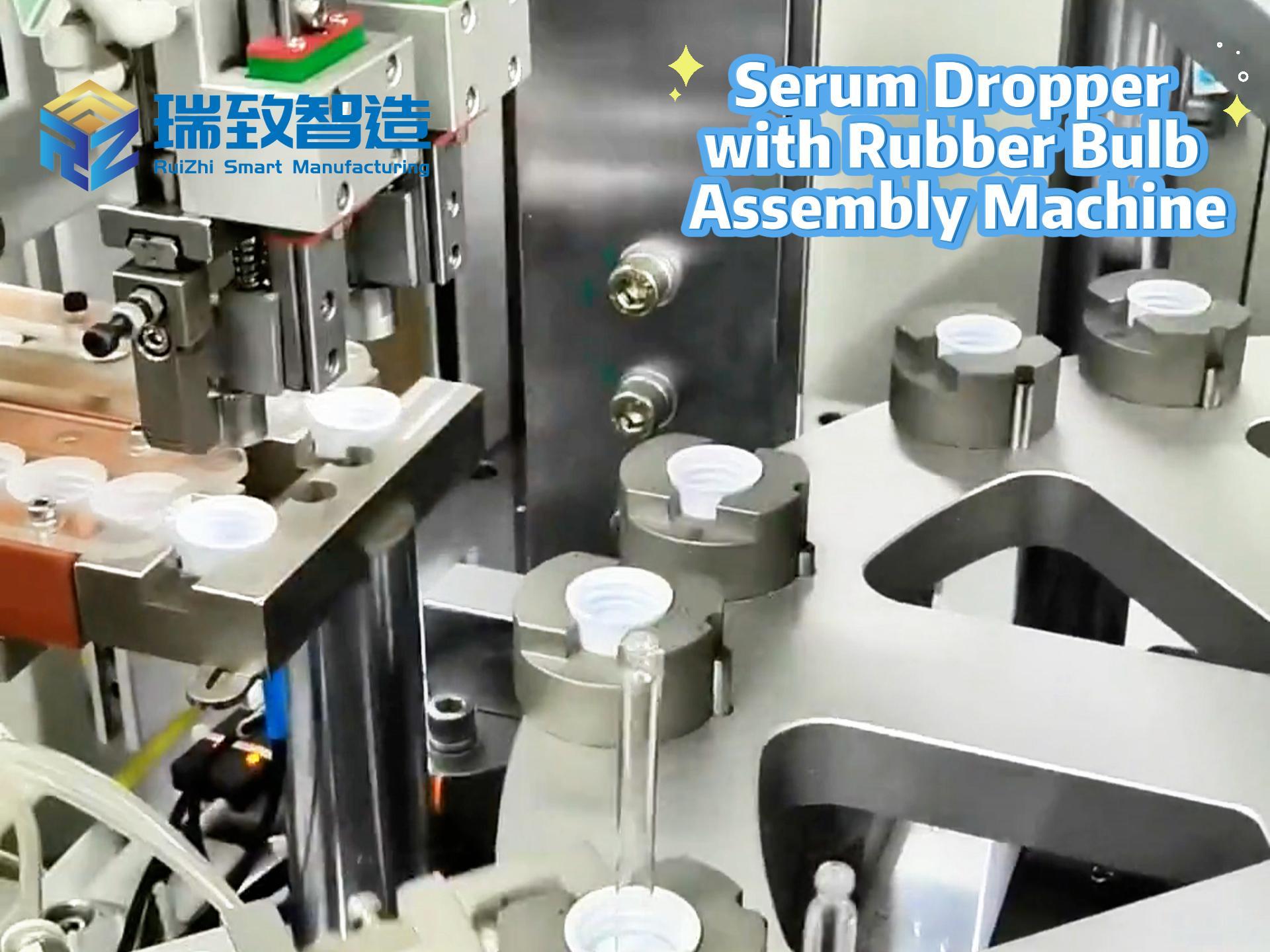
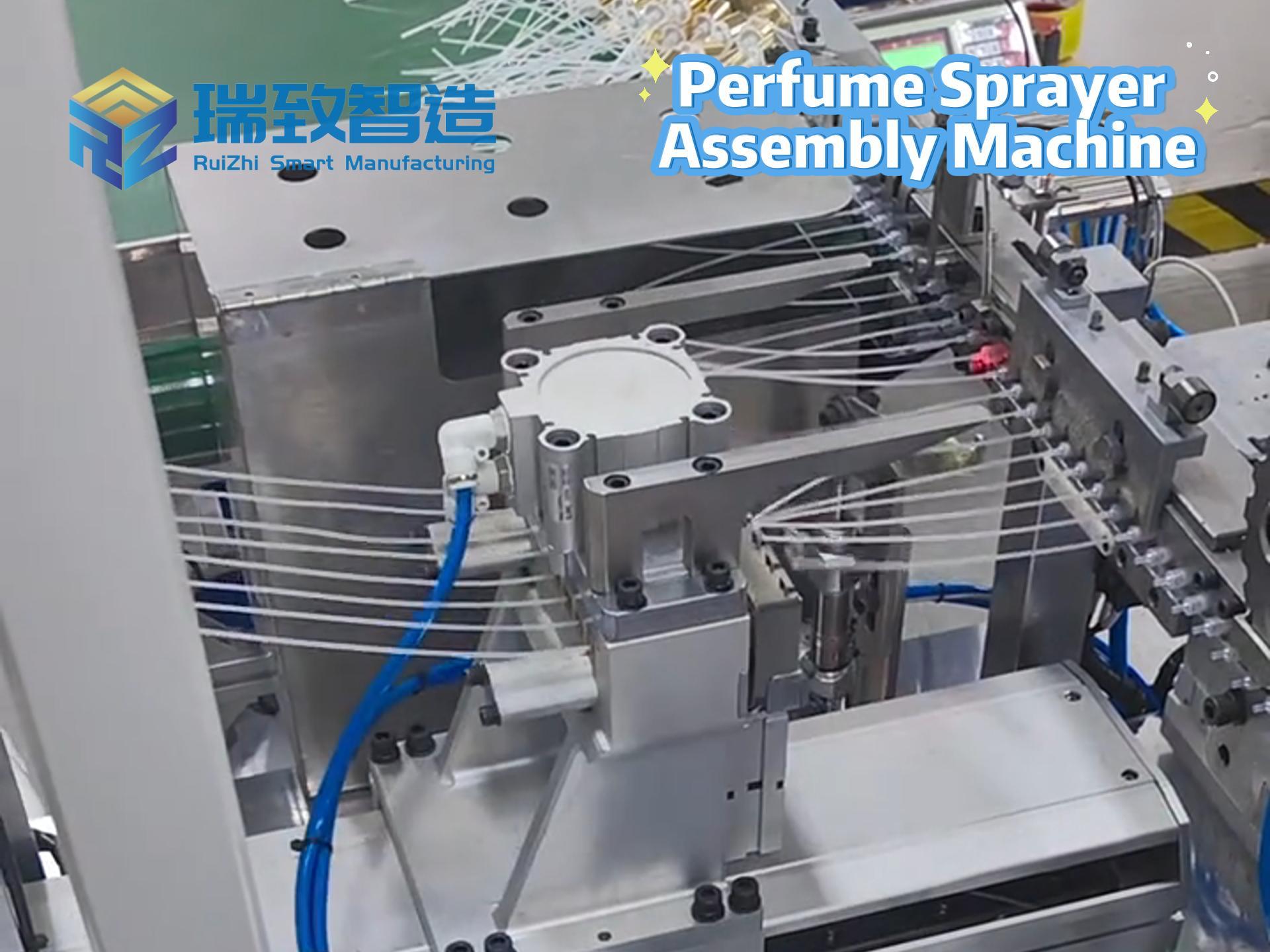
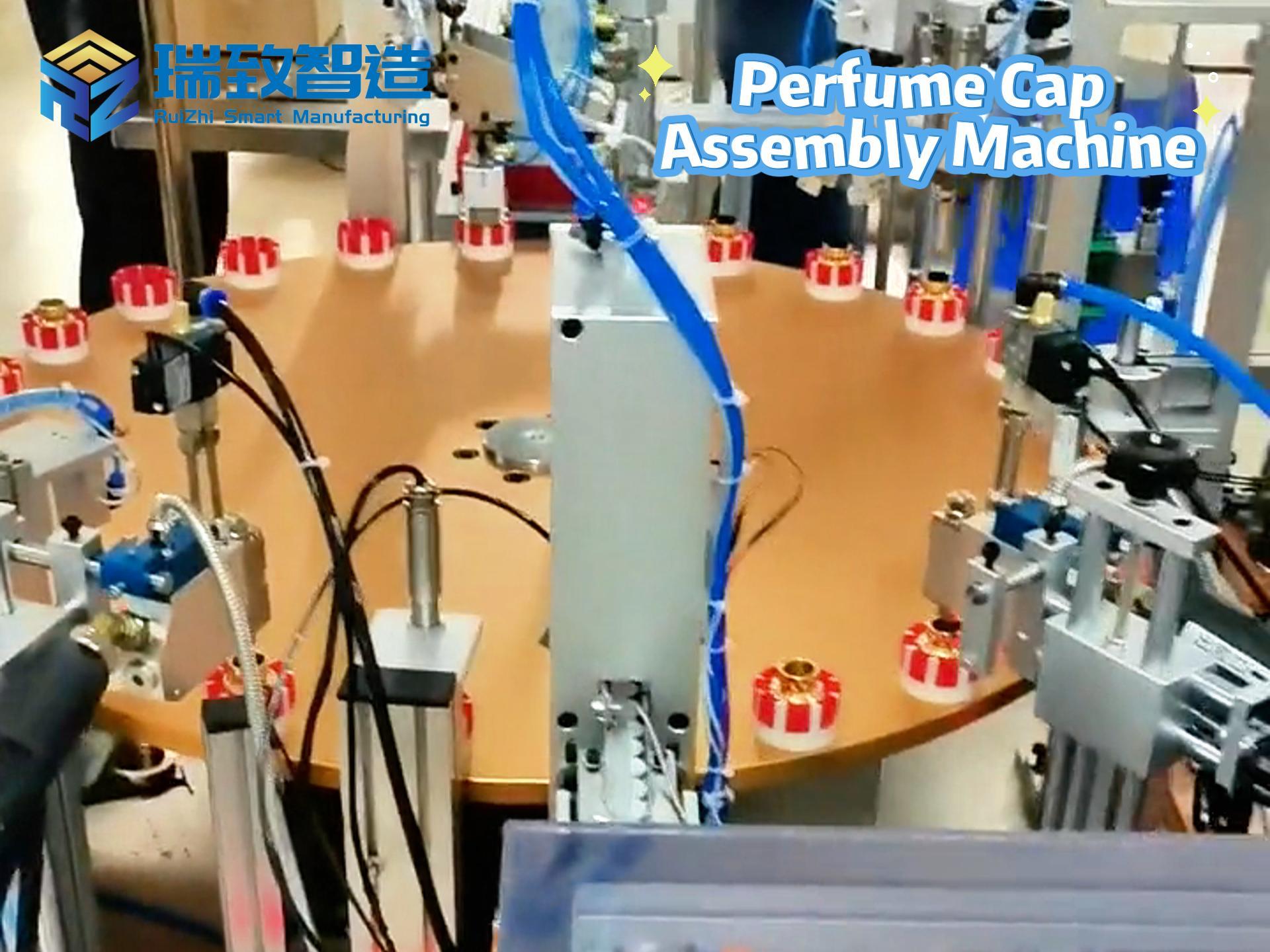
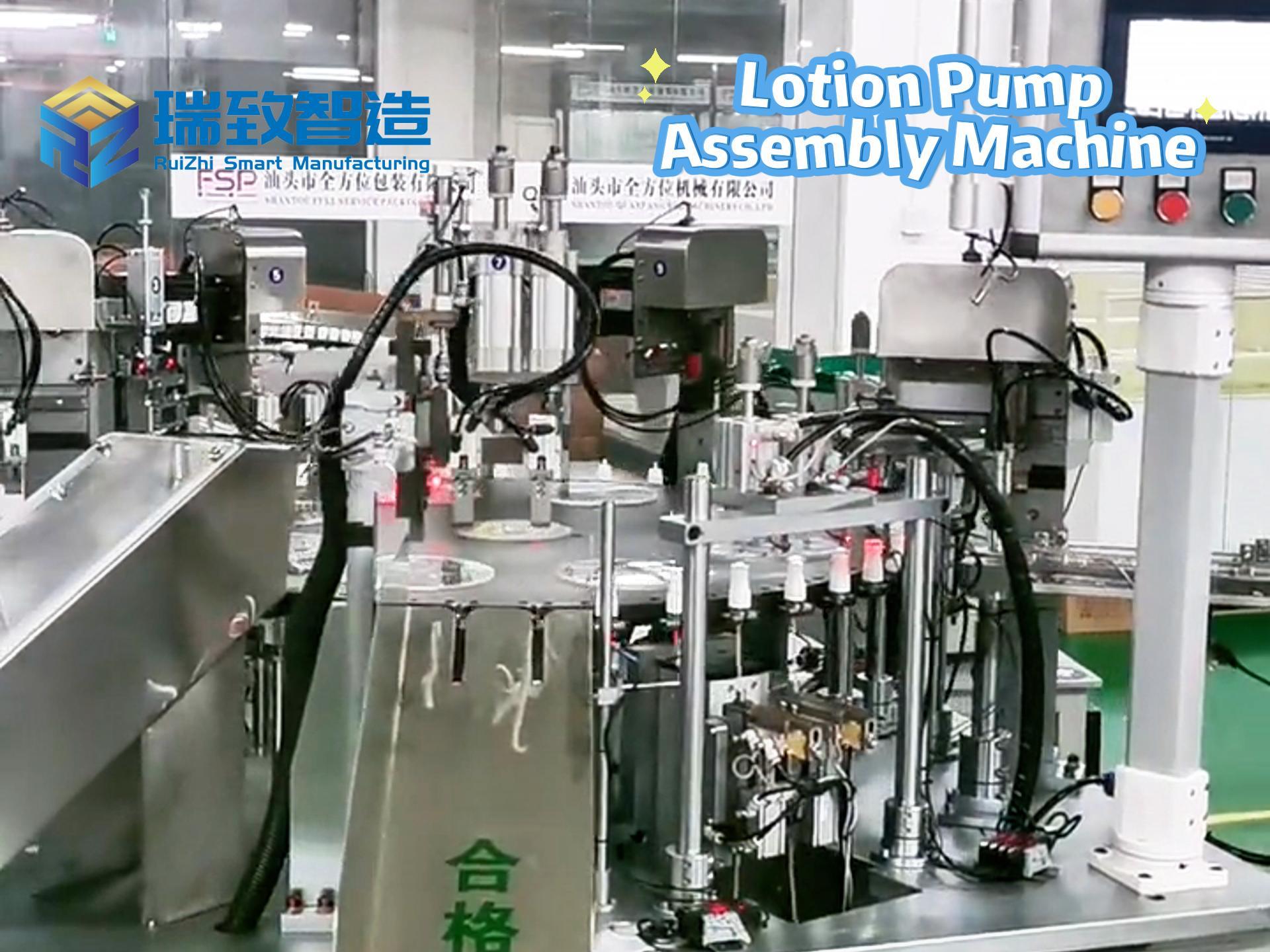
Examples of Robot Automatic Assembly Lines
Advantages of Artificial Intelligence Automatic Assembly Lines